CIP Protocol Hardening: Securing the Industrial Language
Unencrypted traffic exposes your control logic. Learn how deep packet inspection and CIP Security enforce trust without compromising determinism.
Your most critical controllers often cannot be patched. Strategic compensating controls create layered defenses that protect vulnerable legacy PLCs without requiring replacement or downtime.

That rock-solid ControlLogix running your core process cannot be patched—but it can be protected.
Throughout industrial facilities, legacy PLCs form the operational backbone, running processes that cannot tolerate interruption. These controllers - perfectly reliable from a functional perspective - represent massive security liabilities with known vulnerabilities that manufacturers will never address. The conventional cybersecurity approach of "patch and update" fails completely when facing hardware that cannot be modified without risking operational failure. This reality demands a fundamental shift in strategy from eliminating vulnerabilities to containing and monitoring them through external controls.
Isolate what you cannot patch—strategic segmentation contains legacy systems in protected enclaves.
Industrial firewalls from suppliers like Westermo enable the creation of secure enclaves where legacy controllers operate with minimal external exposure. By implementing granular firewall rules that permit only essential communications, organizations can effectively shrink the attack surface available to potential threats. This approach allows legitimate control traffic while blocking unauthorized access attempts, reconnaissance scans, and malicious commands. Proper segmentation ensures that even if other network areas are compromised, legacy systems remain protected behind multiple security boundaries.
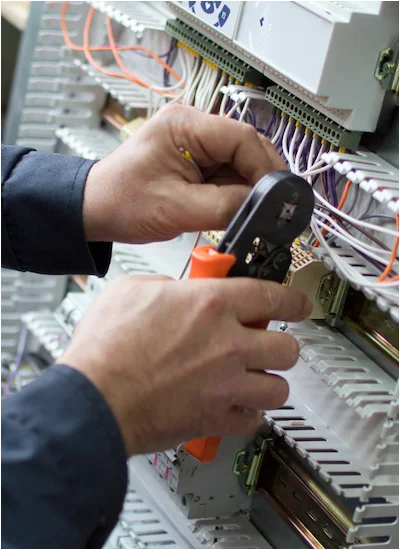
Deep packet inspection distinguishes legitimate control commands from malicious manipulation attempts.
Conventional firewalls see only IP addresses and ports, but industrial firewalls with CIP awareness understand the context of EtherNet/IP communications. This protocol intelligence enables policies that permit routine I/O data exchange while blocking programming mode changes, firmware uploads, or controller stops. Solutions from manufacturers like ProSoft can enforce these application-layer controls, ensuring that legacy controllers continue to function normally while being protected from malicious commands that could disrupt operations. This granular control maintains operational integrity while adding significant security protection.
Fibre's inherent characteristics create natural security boundaries for vulnerable control segments.
The deployment of industrial fibre optics for connections to legacy system enclaves provides both physical and logical separation. Fibre's immunity to EMI ensures communication reliability while preventing electrical-based attacks. More importantly, separate fibre runs create unambiguous physical boundaries that cannot be accidentally bridged. Media converters from suppliers like ATOP enable this physical segmentation while maintaining protocol compatibility. This approach complements logical controls with physical enforcement, creating defense in depth that is particularly valuable for protecting systems that cannot be updated.
Vendor connections represent the most common pathway to legacy system compromise.
Third-party support for legacy systems often requires remote access, creating temporary but critical security gaps. Secure access solutions from suppliers like Secomea ensure that these connections don't bypass other security controls. These systems provide granular session control, detailed auditing, and the ability to restrict vendor access to specific devices and functions. By implementing purpose-built industrial remote access, organizations maintain the support capabilities essential for legacy systems while eliminating the risks associated with conventional VPNs or modem connections.
When you cannot patch vulnerabilities, early detection becomes your most critical defense.
Continuous monitoring of network traffic to and from legacy systems provides early warning of compromise attempts. Advanced monitoring platforms can establish baseline communication patterns for each controller and generate alerts when deviations occur. Unexpected connection attempts, unusual command sequences, or abnormal traffic volumes all indicate potential security incidents. This behavioral monitoring approach is particularly effective for legacy systems because it doesn't rely on signature updates or device modifications - it simply observes and alerts based on understood normal operations.
Separate management networks ensure emergency access even during security incidents.
Legacy systems require special consideration for emergency management, particularly during security incidents that might affect primary network connectivity. Cellular-based out-of-band management solutions from suppliers like Welotec provide secure alternative access paths that remain available even if primary network connections are compromised or intentionally disabled. These separate management channels ensure that security teams can maintain visibility and control during incidents, enabling effective response without requiring physical presence at remote sites.
Proper documentation transforms security measures from technical implementations to compliance assets.
For organizations facing regulatory requirements or audit scrutiny, comprehensive documentation of compensating controls is essential. This documentation should clearly articulate the vulnerability being addressed, the compensating control implemented, and the risk reduction achieved. Well-documented controls demonstrate due care and reasonable security practices, even when legacy systems cannot be updated to current standards. This approach satisfies compliance requirements while maintaining operational continuity with essential legacy equipment.
No single control provides complete protection - layered defenses create resilience through redundancy.
The most effective strategy for securing legacy systems involves implementing multiple overlapping controls. Network segmentation, application filtering, monitoring, and access controls should work together to create a defensive ecosystem where the failure of any single control doesn't result in system compromise. This defense-in-depth approach acknowledges that perfect security is unattainable while creating practical protection that withstands individual control failures or evolving attack techniques.
Compensating controls buy time—but eventual migration to supportable platforms remains essential.
While compensating controls provide immediate protection, they should be implemented as part of a broader strategy that includes eventual system modernization. A structured migration plan identifies the highest-risk legacy systems, establishes replacement priorities, and schedules upgrades during planned maintenance windows. This approach manages risk in the short term while working toward long-term solutions that eliminate the underlying vulnerability of unpatchable systems.
Yes, layered compensating controls can effectively mitigate many specific vulnerabilities by blocking exploit attempts, containing potential breaches, and detecting anomalous activity patterns associated with known attack methods.
Phased implementation during planned maintenance windows allows careful testing of communication paths before enforcement. Monitoring modes can verify all required traffic patterns before activating blocking rules.
Well-implemented compensating controls can typically extend the secure lifespan of legacy systems by 3-5 years, providing adequate time for planned migration while maintaining acceptable risk levels.
Properly implemented industrial security controls have minimal performance impact. Industrial-grade equipment from suppliers like Westermo is designed to maintain deterministic performance while providing security functions.
While basic segmentation can be implemented internally, comprehensive compensating control strategies typically benefit from specialist expertise to ensure proper configuration and avoid operational disruption.
Properly documented compensating controls are explicitly recognized in most industrial security standards as acceptable alternatives when direct vulnerability remediation is not possible.
Connection attempts from unauthorized sources, programming mode changes, firmware upload attempts, and abnormal command sequences provide the most valuable detection capabilities for protected legacy systems.
The presence of unpatchable legacy systems doesn't have to mean unacceptable security risk. Through strategic implementation of compensating controls, organizations can create effective protection that addresses specific vulnerabilities while maintaining operational continuity. This approach transforms unmanageable risk into carefully controlled, monitored, and documented risk.
Security is not about eliminating all vulnerabilities - it's about managing risk to acceptable levels. For legacy systems, this means creating layers of protection that compensate for inherent weaknesses while enabling essential operations to continue safely.
Contact a Throughput security specialist for a legacy system assessment and receive our Compensating Controls Framework.
Subscribe to the Link & Layer | Smart Learning Hub for immediate access to our "Legacy System Security Guide" with implementation templates and policy examples.
Don't let unpatchable systems become your weakest link. Build defenses that compensate for inherent vulnerabilities.
Unencrypted traffic exposes your control logic. Learn how deep packet inspection and CIP Security enforce trust without compromising determinism.
Default credentials and outdated firmware make switches your weakest link. Discover how systematic hardening restores integrity to industrial networks.