The "Inherently Secure" Myth:
Real Threats to Industrial Fibre
The dangerous assumption that fibre cannot be tapped leaves critical control networks exposed to physical and optical layer attacks that bypass conventional security measures.
Complacency is the First Vulnerability to Address
The belief that fibre is immune to interception creates a false sense of security that attackers readily exploit.
While fibre optics don't radiate electromagnetic signals like copper cabling, this physical characteristic has been misinterpreted as comprehensive security. This misconception leads to inadequate protection of critical infrastructure, where fibre runs are treated as secure by default rather than being properly monitored and protected. The reality is that fibre networks face unique threats at the physical and data link layers that require specialized security measures. Organisations that assume their fibre backbone is inherently protected often neglect basic security controls, creating vulnerable pathways directly into the heart of their control systems.
Optical Tapping Extracts Data Without Detection
A carefully placed fibre bend can leak enough light to capture every command passing through a critical control link.
Fibre optic cables transmit data using light pulses through glass or plastic fibres. While the signal remains contained under normal conditions, intentional manipulation can extract these light pulses without breaking the connection or triggering alarms. Bend tapping devices clamp onto the fibre cable, creating a precise curvature that causes a small portion of light to escape. This leaked light can be captured and converted back into electrical signals, revealing all transmitted data. More sophisticated methods involve cutting and splicing taps that are virtually undetectable without specialized optical testing equipment. These attacks are particularly dangerous because they occur outside the digital domain, bypassing encryption and intrusion detection systems that monitor network traffic.
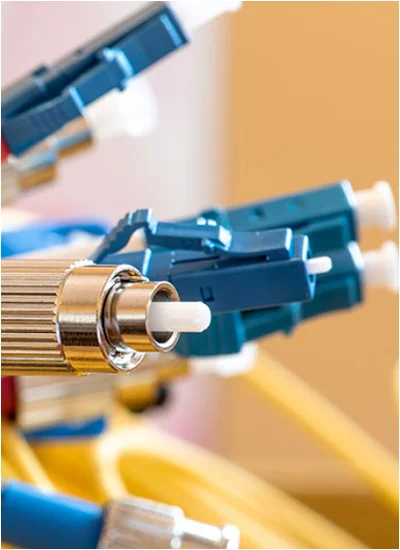
Rogue Transceivers Create Backdoors at the Connection Point
A compromised SFP module can provide persistent access while appearing as legitimate network hardware.
Small Form-factor Pluggable (SFP) transceivers represent a critical vulnerability in fibre optic networks. These modular components convert electrical signals to optical ones and vice versa, but they contain firmware and processing capabilities that can be manipulated. Malicious transceivers can be programmed to copy and retransmit traffic, create hidden administrative access points, or even manipulate data in transit. Because these devices operate at the physical layer, they can bypass network security controls and remain undetected by conventional monitoring systems. The widespread availability of third-party SFPs with questionable security pedigrees makes this an accessible attack vector for sophisticated threat actors targeting industrial infrastructure.
Light Injection Attacks Manipulate Control Systems
False optical signals can overwrite legitimate commands or disrupt communications entirely.
Where tapping extracts information, injection attacks manipulate system behaviour by introducing malicious optical signals into the fibre network. By splicing into a fibre line or exploiting poorly secured connection points, attackers can inject fabricated control commands that appear legitimate to receiving devices. This could include commands to alter setpoints, disable safety systems, or initiate emergency shutdowns. More subtle attacks might introduce timing delays or packet corruption that destabilizes control loops without immediately revealing malicious intent. These attacks are particularly effective against legacy industrial equipment that lacks cryptographic authentication of commands.
The Conversion Layer Creates Critical Attack Surfaces
Media converters bridge the optical and electrical domains, creating vulnerable translation points in the network.
Fibre optic networks frequently connect to electronic devices through media converters, which translate between optical and electrical signalling. These devices often represent the weakest security link in the infrastructure. Many industrial media converters lack basic security features, operating with default credentials, unencrypted management interfaces, and outdated firmware with known vulnerabilities. When compromised, they can provide a pivot point between segregated network zones or be used to intercept and manipulate traffic passing between fibre and copper segments. Hardened converters from manufacturers like ATOP incorporate essential security features, but many facilities continue to operate with basic commercial-grade equipment that was never designed for secure industrial applications.
Physical Infrastructure Provides Multiple Attack Vectors
Unsecured patch panels and distribution frames offer easy access to the optical backbone.
The physical infrastructure supporting fibre networks presents numerous exploitation opportunities. Patch panels in unsecured communications closets allow attackers to easily reroute or tap connections. Unlabelled or poorly documented fibre runs make unauthorized connections difficult to detect. Slack fibre loops left in cabinets provide material for covert tapping without affecting operational links. Even the fibre itself can be vulnerable—some types of fibre are more susceptible to bending attacks, and ageing cables may develop micro-fractures that both weaken signals and create opportunities for interception. Without proper physical security controls and regular optical integrity verification, these vulnerabilities remain invisible until exploited.
Optical Time-Domain Reflectometry Reveals Hidden Compromises
Specialized fibre testing can detect unauthorized access points and physical tampering.
Optical Time-Domain Reflectometers (OTDR) send light pulses through fibre cables and measure the reflected signals to characterize the entire length of the link. This technology can identify the precise location of bends, splices, and connection points that shouldn't exist. Regular OTDR testing establishes a baseline of normal fibre characteristics, with subsequent comparisons revealing changes that might indicate tampering. Advanced systems can even detect the distinctive signature of specific tapping methods. While traditionally used for maintenance and fault location, OTDR technology represents a powerful security tool when applied systematically across critical fibre infrastructure.
Comprehensive Monitoring Detects Anomalous Optical Patterns
Continuous monitoring of optical power levels can reveal tampering that would otherwise go unnoticed.
Sophisticated fibre security extends beyond periodic testing to continuous monitoring of optical characteristics. Unexplained changes in signal loss, the appearance of new reflections, or subtle power variations can indicate manipulation attempts. By establishing normal operating baselines for each fibre link, monitoring systems can alert security teams to anomalies that warrant investigation. This approach can detect attacks in progress, potentially enabling intervention before significant damage occurs. Industrial switches from suppliers like Westermo can incorporate optical monitoring capabilities alongside their networking functions, providing integrated security without additional infrastructure.
Defence Begins with Physical Access Control
The most sophisticated optical protections are useless if attackers can physically reach the fibre infrastructure.
Preventing fibre attacks requires controlling physical access to every point where the optical network could be manipulated. This includes communications cabinets, patch panels, splice enclosures, and even the fibre runs themselves in vulnerable areas. Access control systems, surveillance cameras, and tamper-evident seals provide basic protection, while more critical infrastructure may require intrusion detection sensors on communications cabinets and regular physical inspection of fibre routes. The principle of defence in depth applies equally to physical security - multiple layers of protection ensure that a single failure doesn't expose the entire optical infrastructure to compromise.
Encryption Renders Intercepted Data Useless
While not preventing interception, cryptographic protection ensures that tapped information remains meaningless.
Encryption represents the final layer of defence for fibre optic communications. Even if attackers successfully tap a fibre link, encrypted traffic remains protected against interpretation or manipulation. MACsec (Media Access Control Security) operates at the data link layer, providing encryption and authentication for all traffic between network devices. This technology is increasingly available in industrial networking equipment and can be implemented without impacting deterministic performance requirements. When combined with physical security measures and optical monitoring, encryption creates a comprehensive defence strategy that addresses both the unique vulnerabilities of fibre and conventional network security threats.
Supply Chain Integrity Prevents Hardware Compromise
Verifying the authenticity and security of optical components closes a critical vulnerability vector.
The security of fibre optic infrastructure depends on the integrity of every component in the signal path. Counterfeit or maliciously modified transceivers, media converters, and other optical equipment can introduce vulnerabilities at the point of installation. Establishing trusted supplier relationships, verifying component authenticity, and maintaining secure inventory controls prevents these threats from entering the operational environment. Working with established industrial suppliers like Westermo and ATOP ensures components designed and manufactured with security considerations, rather than repurposed commercial equipment with unknown security properties.
Answered - Some Frequently Asked Questions
With proper equipment and physical access, tapping fibre is straightforward for knowledgeable attackers. Commercial fibre tapping kits are available, and the techniques are well-documented in telecommunications security literature.
Yes, the physical tapping process works regardless of encryption. However, encrypted traffic appears as random data without the cryptographic keys, rendering the intercepted information useless for understanding or manipulation.
Critical infrastructure should undergo baseline OTDR testing during installation, with follow-up tests quarterly or after any physical work near fibre runs. Continuous optical monitoring can supplement periodic testing for high-security applications.
Single-mode fibre generally offers better security characteristics than multi-mode due to its smaller core diameter, which makes successful tapping more difficult. However, no fibre type is truly tap-proof without additional protective measures.
Typically not. Fibre tapping occurs at the physical layer and usually doesn't generate the network-level anomalies that traditional security monitoring detects. Specialized optical monitoring is required.
Unsecured media converters represent the most common vulnerability, as they often lack basic security features and provide a bridge between network segments that might otherwise be isolated.
Remote sites require comprehensive physical security measures, including monitored intrusion detection systems, regular physical inspections, and optical monitoring capable of alerting to tampering attempts. Secure remote access solutions from suppliers like Secomea can provide controlled access without exposing the underlying infrastructure.
From Assumption to Assurance
The myth of inherent fibre security represents one of the most dangerous misconceptions in industrial network design. By recognizing the very real threats at the optical layer and implementing appropriate physical, monitoring, and cryptographic controls, organizations can transform their fibre infrastructure from a assumed safeguard into a verified secure foundation.
The transition begins with acknowledging the vulnerability and proceeds through systematic implementation of defences that address both conventional network threats and the unique challenges of optical communications.
Ready to move beyond security assumptions?
Contact a Throughput security specialist for a fibre vulnerability assessment and receive our Optical Security Implementation Framework.
Subscribe to the Link & Layer | Smart Learning Hub for immediate access to our "Fibre Security Checklist" including OTDR testing procedures and hardening guides.
Don't let dangerous assumptions undermine your network security. Build your defences on verified protection rather than mistaken beliefs.
You May Also Be Interested In ...
Industrial Network Vulnerabilities: Hidden Risks
Unmanaged media converters, patch panels, and switches silently expose industrial networks to attack. Simple, overlooked devices create hidden vulnerabilities - securing them with trusted hardware and monitoring transforms weak points into strong defences.
AI Fibre Monitoring: Predictive OT Security
AI-driven fibre monitoring transforms industrial networks by predicting failures and detecting physical tampering before they occur. Continuous, real-time analysis identifies subtle degradations and breaches, ensuring unmatched reliability and security.
OT Network Encryption: Security vs Determinism
Securing industrial fibre no longer means sacrificing real-time control. Layer 2 encryption like MACsec preserves microsecond-level determinism, letting engineers protect critical data without disrupting safety-critical operations.