Designing Zero-Recovery Fibre Rings:
PRP, HSR & RSTP for Sub-10ms Failover in Critical OT
Single Points of Failure Have No Place in Critical Infrastructure
The moment a network failure impacts control logic, your redundancy strategy has already failed.
Industrial processes in power generation, chemical manufacturing, and water treatment cannot tolerate communication interruptions that disrupt control cycles or safety systems. Traditional network redundancy approaches that involve seconds of recovery time are fundamentally inadequate for applications where sub-10ms response is mandatory. The consequence of delayed failover isn't merely inconvenience - it's process shutdown, equipment damage, or safety incidents. True zero-recovery networking requires architectures where redundancy is active and continuous, not reactive and disruptive.
Parallel Redundancy Protocol Eliminates the Concept of Failover
PRP's simultaneous transmission approach means receiving devices never experience network failure.
The Parallel Redundancy Protocol represents the gold standard for industrial network resilience. Rather than detecting failures and switching to backup paths, PRP networks transmit duplicate frames simultaneously through two completely independent networks. Receiving devices process the first arrival and discard the duplicate, creating a system where single network failures have zero impact on communications. This architecture eliminates the recovery time entirely, making it ideal for safety systems and critical control loops where even milliseconds of interruption are unacceptable. Implementing PRP requires careful network design but delivers absolute protection against single points of failure.
High-availability Seamless Redundancy Optimizes for Deterministic Environments
HSR networks eliminate recovery time by treating redundancy as an integral system characteristic rather than a backup feature.
Similar to PRP in concept, High-availability Seamless Redundancy operates on ring topologies where each device transmits frames in both directions simultaneously. This approach eliminates switches from the redundancy equation, creating deterministic networks where redundancy is built into the communication pattern itself. HSR is particularly valuable in applications like substation automation and process control where the predictable performance of ring topologies aligns with operational requirements. The protocol's deterministic characteristics make it suitable for the most demanding applications where communication timing must be absolutely predictable under all conditions, including network failures.
Rapid Spanning Tree Protocol Delivers Cost-Effective Resilience
When absolute zero-recovery isn't mandatory, RSTP provides substantial improvement over traditional networks.
For applications where brief communication interruptions are acceptable but extended outages are not, Rapid Spanning Tree Protocol offers a practical balance between cost and resilience. Modern implementations can achieve sub-50ms convergence times in properly configured networks, representing a significant improvement over traditional STP's 30-50 second recovery periods. While not suitable for safety systems or high-speed control, RSTP provides adequate protection for supervisory networks, data collection systems, and non-critical control applications. The protocol's widespread support across industrial networking equipment makes it accessible for organizations with mixed criticality requirements.
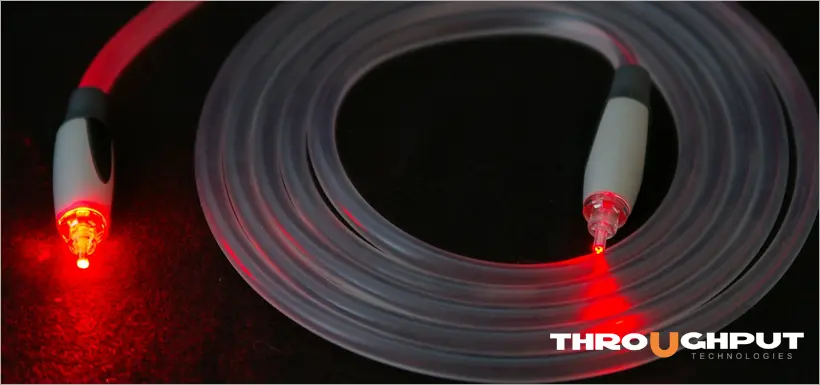
Fibre Optics Enable the Physical Layer for Deterministic Redundancy
The inherent characteristics of fibre make it the only viable medium for true zero-recovery networks.
Copper-based redundancy schemes face fundamental limitations that fibre optics inherently overcome. Fibre's immunity to electromagnetic interference eliminates a major category of transient failures that can trigger unnecessary network reconvergence. The consistent signal propagation characteristics ensure that redundant paths maintain predictable latency relationships. Longer distance capabilities enable geographically diverse redundant paths that protect against physical damage to cable routes. These characteristics make fibre the essential foundation for networks where redundancy must be both absolute and predictable.
Dual-Homed Architectures Complete the End-to-End Protection Strategy
Network redundancy means nothing if end devices can't leverage multiple communication paths.
The most sophisticated network redundancy can be defeated by single-homed devices that represent points of failure. True zero-recovery architectures require dual-homed devices with independent network interfaces connected to separate network infrastructure. This approach extends redundancy from the network core to the edge devices that actually execute control logic. Industrial controllers and networking equipment from manufacturers like Westermo support dual-homing capabilities that seamlessly transition between network connections without application disruption. This end-to-end approach ensures that redundancy protects the entire communication path, not just the network backbone.
Deterministic Performance Requirements Dictate Protocol Selection
The choice between redundancy protocols depends entirely on your application's tolerance for interruption.
Selecting the appropriate redundancy technology requires understanding the actual consequences of communication failure. Safety systems and motion control typically demand PRP or HSR where any interruption is unacceptable. Process control systems might tolerate RSTP's brief convergence if control algorithms can maintain stability through transient communication loss. Supervisory systems and data historians might function adequately with traditional redundancy approaches. This application-aware selection process ensures that organizations invest appropriately based on operational risk rather than implementing one-size-fits-all solutions.
Implementation Strategy Balances Protection and Complexity
Phased deployment allows organizations to build expertise while delivering incremental resilience improvements.
Transitioning to zero-recovery networks doesn't require immediate organization-wide implementation. Beginning with the most critical systems allows teams to develop implementation expertise while delivering maximum risk reduction. A typical progression might start with RSTP implementation across the entire network, then progress to PRP or HSR for specific high-criticality applications. This approach manages both cost and complexity while building organizational capability gradually. Each phase delivers measurable resilience improvements that justify subsequent investments in more sophisticated protection.
Monitoring and Validation Ensure Continuous Protection
Redundancy that isn't regularly tested represents theoretical rather than actual protection.
The complex interaction between redundancy protocols and control systems requires continuous monitoring to ensure protection remains effective. Network management systems must track redundancy status, path performance, and failover events. Regular testing through controlled failure simulation validates that redundancy mechanisms function as designed without disrupting operations. Industrial switches from suppliers like Westermo provide detailed redundancy monitoring capabilities that integrate with network management systems, ensuring that protection doesn't degrade over time through configuration drift or component failure.
Cybersecurity Considerations Extend to Redundant Paths
Network redundancy must not become a vulnerability multiplication mechanism.
Dual network paths double the potential attack surface if not properly secured. Redundant networks require consistent security policies, monitoring, and access controls across all paths. Encryption technologies like MACsec must be implemented on both networks to prevent redundancy from creating security gaps. Remote access solutions from manufacturers like Secomea ensure that maintenance connections don't bypass redundancy protections. This integrated approach to security and resilience ensures that networks remain both available and protected under all conditions.
The Business Case Extends Beyond Uptime Statistics
The value of zero-recovery networking transcends simple availability metrics.
While reduced downtime provides obvious financial benefits, the true value of zero-recovery networking includes prevented safety incidents, avoided environmental releases, and maintained product quality. In many process industries, the cost of an unplanned shutdown dwarfs the investment in network resilience. Furthermore, the operational confidence enabled by reliable communications allows organizations to implement more advanced automation strategies that depend on absolutely reliable data exchange. This transforms network resilience from a cost centre into an enabler of operational excellence.
Answered - Some Frequently Asked Questions
True zero-recovery protocols like PRP and HSR prevent applications from experiencing any communication interruption. Sub-10ms failover means applications might experience a brief interruption but recover quickly enough to maintain process stability.
Yes, hybrid approaches are common. Critical control loops might use PRP while supervisory networks use RSTP. Proper network segmentation ensures these different approaches operate without interference.
PRP operates at the data link layer, so applications remain completely unaware of the redundancy mechanism. The network interface handles duplicate detection and elimination transparently.
PRP requires completely redundant network infrastructure, essentially doubling network costs. RSTP leverages existing network topology more efficiently, typically adding 20-30% to network costs.
Controlled testing during planned maintenance windows validates redundancy mechanisms. Modern industrial switches allow testing of individual links without triggering network-wide reconvergence.
Yes, single-mode fibre with appropriate transceivers can span tens of kilometres. For longer distances, fibre extension devices from suppliers like FlexDSL can maintain signal integrity over hundreds of kilometres.
The most critical systems typically implement redundancy at both levels. Dual-redundant controllers connected to redundant networks provide comprehensive protection against both device and network failures.
From Redundancy to Resilience
True network resilience means that failures occur without impact - not that systems recover quickly after impact. The distinction separates adequate infrastructure from exceptional infrastructure that enables operational excellence rather than merely preventing disaster.
By implementing appropriate redundancy technologies matched to application requirements, organizations transform their networks from potential points of failure into foundations of operational certainty.
Ready to design networks that withstand any single failure?
Contact a Throughput network specialist for a resilience assessment and receive our Redundancy Implementation Framework.
Subscribe to the Link & Layer | Smart Learning Hub for immediate access to our "Network Resilience Design Guide" with protocol selection matrices and configuration templates.
Don't settle for networks that recover from failure. Build networks that operate through failure.
You May Also Be Interested In ...
Deterministic Networking: Beyond Bandwidth in OT
In industrial networks, determinism - not raw speed - ensures reliability. Predictable timing, low jitter, and synchronized control loops, supported by TSN and fibre optics, prevent safety incidents and maintain operational continuity.
Industrial Fibre Security Myths: Beyond Tap-Proof
Fibre isn’t inherently secure; physical attacks, rogue transceivers, and insecure media converters threaten industrial networks. True protection requires controlled access, continuous monitoring, and trusted hardware with layered security measures.
Industrial Network Vulnerabilities: Hidden Risks
Unmanaged media converters, patch panels, and switches silently expose industrial networks to attack. Simple, overlooked devices create hidden vulnerabilities - securing them with trusted hardware and monitoring transforms weak points into strong defences.