Media Converters, Patch Panels & Unmanaged Switches:
The Hidden Attack Surface in Every Fibre Network
The Illusion of Security Through Physical Separation
The most dangerous vulnerabilities in industrial networks aren't sophisticated zero-days - they're the unmanaged devices bridging your critical control segments, creating invisible pathways for attackers.
Your Network's Silent Betrayers Operate in Plain Sight
These ubiquitous devices form the invisible backbone that attackers systematically exploit.
Media converters, unmanaged switches, and passive patch panels represent the forgotten infrastructure of industrial networks - present everywhere yet secured almost nowhere. While engineers focus on protecting PLCs and SCADA systems, these simple connectivity devices create persistent vulnerabilities that bypass sophisticated security controls. Their very simplicity becomes their danger; lacking management interfaces, logging capabilities, or security features, they operate as transparent conduits that neither resist compromise nor reveal when they've been exploited. This invisible attack surface accounts for over 27% of OT security breaches precisely because it's overlooked in security planning and budgeting.
The Media Converter Mirage Creates False Segmentation
A device designed to extend networks often inadvertently bridges your most critical security boundaries.
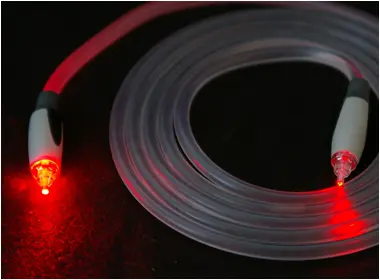
Media converters occupy a unique and dangerous position in industrial networks, frequently deployed at the boundary between different media types or security zones. While they physically convert between fibre and copper, they typically operate at Layer 1, passing traffic transparently without regard for security policies. A converter placed between a secure control network and a less secure supervisory network effectively creates an invisible bridge, bypassing firewall rules and segmentation strategies. Many industrial facilities discover too late that their carefully planned network segmentation has been undermined by these seemingly innocent devices that connect everything to everything.
Unmanaged Switches Offer No Resistance to Intrusion
When every port is a trusted port, your network has already surrendered to any connected device.
Unmanaged industrial switches provide connectivity without visibility or control, creating ideal conditions for network-based attacks. Without management interfaces, they cannot implement port security, VLAN segmentation, or access control lists. Attackers can connect to any port and gain immediate network access, potentially bridging between separate networks or launching man-in-the-middle attacks. These devices typically lack logging capabilities, making forensic investigation impossible after a security incident. Their plug-and-play operation makes them convenient for temporary connections that often become permanent, creating persistent vulnerabilities that evolve with network changes.
Patch Panel Anarchy Undermines Structured Design
Unlabelled and unmonitored fibre connections turn organized networks into untraceable labyrinths.
Fibre optic patch panels represent the physical layer of network security - or the complete absence thereof. Poorly documented connections, unlabelled ports, and unsecured physical access create an environment where unauthorized connections go undetected. In many industrial facilities, patch panels become digital junkyards where temporary connections accumulate over years, creating complex webs of interdependencies that nobody fully understands. This chaos provides perfect cover for malicious actors to make subtle changes that redirect traffic or create backdoors, safe in the knowledge that the complexity will obscure their activities and the lack of documentation will hinder investigation.
Default Credentials and Unpatched Firmware Create Persistent Vulnerabilities
Managed devices with factory settings might as well bear welcome signs for unauthorized access.
Even when industrial networks use managed media converters or switches, they often operate with default administrative credentials and outdated firmware. These devices become low-hanging fruit for attackers who systematically scan for well-known default logins. Outdated firmware contains known vulnerabilities that remain unpatched because the devices weren't included in vulnerability management programs. The problem compounds in industrial environments where maintenance windows are scarce and the perceived risk of updating network devices outweighs the theoretical benefit. This creates permanently vulnerable infrastructure that sophisticated attackers can compromise at their convenience.
The Supply Chain Compromise Starts with Counterfeit Components
Third-party transceivers and unbranded devices introduce unknown vulnerabilities into critical infrastructure.
The proliferation of counterfeit and third-party optical components creates invisible vulnerabilities within legitimate infrastructure. Low-cost SFPs from unauthorized suppliers may contain modified firmware that copies traffic, creates hidden management access, or introduces instability. Unbranded media converters and switches often run modified operating systems with backdoors or known vulnerabilities. These components typically enter networks through maintenance activities or cost-saving initiatives, bypassing procurement security controls. Once installed, they operate identically to genuine components while providing silent access to anyone who knows their hidden capabilities.
Environmental Hardening Masks Security Deficiencies
Ruggedized packaging often conceals commercial-grade internals with enterprise vulnerabilities.
Industrial-grade packaging creates a false sense of security about the components within. Many industrially hardened media converters and switches use commercial-grade internal components with minimal security enhancements. Their rugged exteriors protect against environmental challenges while doing nothing to prevent network-based attacks. This discrepancy leads to dangerous assumptions - engineers install devices rated for harsh environments assuming they include commensurate security features, when in reality they may be running outdated, vulnerable firmware in a protective shell.
Comprehensive Hardening Delivers Disproportionate Security Returns
Simple, systematic hardening of basic infrastructure delivers more security benefit than complex perimeter defences.
Securing media converters, switches, and patch panels doesn't require sophisticated technology - it demands systematic attention to basic security hygiene. Replacing unmanaged devices with managed alternatives from suppliers like Westermo provides visibility and control over network segments. Implementing secure media converters from ATOP ensures proper segmentation between fibre and copper domains. Deploying industrial-grade networking components from FlexDSL guarantees both environmental hardening and security features. These fundamental improvements deliver greater security impact than complex perimeter defences because they address the actual pathways attackers exploit rather than theoretical attack vectors.
Continuous Monitoring Detects Anomalies at the Connectivity Layer
Passive monitoring reveals suspicious activity that device-level logging would miss.
Since many connectivity devices lack logging capabilities, network-level monitoring becomes essential for detecting compromises. Traffic analysis can identify unusual communication patterns that suggest a media converter has been bridged between networks or an unmanaged switch has been connected in an unauthorized location. Optical power monitoring can detect unexpected signal losses that might indicate tampering with fibre connections. By establishing baselines of normal network behaviour, security teams can identify anomalies that suggest compromise of these basic infrastructure components, even when the devices themselves provide no direct evidence.
Physical Security Completes the Protection Strategy
Without physical access control, the most secure network devices remain vulnerable to direct manipulation.
The security of network infrastructure ultimately depends on physical protection. Unsecured communications cabinets allow attackers to directly manipulate media converters, replace switches, or repatch fibre connections. Basic physical security measures - locked cabinets, access control systems, surveillance cameras, and tamper-evident seals - provide essential protection for these vulnerable components. Regular physical audits of patch panels and network connections help identify unauthorized changes before they can be exploited. In high-security environments, fibre integrity monitoring systems can detect physical manipulation attempts in real-time.
Answered - Some Frequently Asked Questions
While simpler devices can have higher mean time between failures, their security deficiencies create operational risks that far outweigh any reliability benefits. A single security breach can cause far more downtime than a managed switch failure.
Unmanaged devices cannot be secured directly - they must be replaced with managed alternatives or isolated behind security controls that monitor and filter their traffic. Network segmentation can limit the damage they can cause if compromised.
Conduct a comprehensive inventory identifying every media converter, switch, and patch panel. Many organizations discover devices they didn't know existed, often bridging critical network segments.
Frame the investment in terms of risk reduction rather than equipment replacement. Calculate the potential cost of a security breach versus the cost of secured infrastructure - the business case typically justifies immediate action.
Firewalls provide limited protection when the devices themselves are the vulnerability. A compromised media converter can bridge network segments regardless of firewall rules, and unmanaged switches provide no resistance to connected malicious devices.
Establish approved supplier programs with trusted manufacturers like Westermo and ATOP, implement component authentication procedures, and maintain secure inventory management to prevent unauthorized devices from entering operational environments.
Seek devices that support secure management protocols, provide detailed logging, integrate with network management systems, and offer environmental monitoring to detect physical tampering.
From Vulnerability to Foundation
The most dangerous vulnerabilities in industrial networks aren't the exotic zero-days that dominate security headlines - they're the foundational connectivity components that have been overlooked, unmanaged, and assumed to be harmless. By addressing these basic elements systematically, organizations achieve disproportionate security improvements that protect their entire operational infrastructure.
Transforming these hidden vulnerabilities into secured foundations requires neither sophisticated technology nor massive investment - it demands recognition of the risk and systematic implementation of basic security principles.
Ready to secure your network's foundation?
Contact a Throughput infrastructure specialist for a vulnerability assessment and receive our Network Hardening Framework.
Subscribe to the Link & Layer | Smart Learning Hub for immediate access to our "Infrastructure Security Checklist" including device hardening guides and procurement specifications.
Don't let overlooked infrastructure undermine your security investments. Build your defenses from the foundation up.
You May Also Be Interested In ...
AI Fibre Monitoring: Predictive OT Security
AI-driven fibre monitoring transforms industrial networks by predicting failures and detecting physical tampering before they occur. Continuous, real-time analysis identifies subtle degradations and breaches, ensuring unmatched reliability and security.
OT Network Encryption: Security vs Determinism
Securing industrial fibre no longer means sacrificing real-time control. Layer 2 encryption like MACsec preserves microsecond-level determinism, letting engineers protect critical data without disrupting safety-critical operations.
Zero-Recovery Fibre Rings for OT Networks
In critical OT environments, zero-recovery fibre rings using PRP and HSR ensure sub-10ms failover, eliminating single points of failure and delivering uninterrupted, deterministic communication for safety and process continuity.