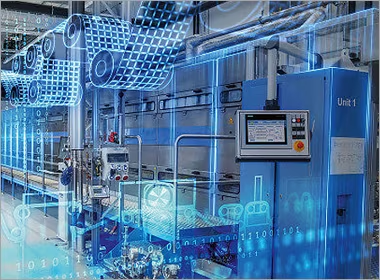
Engineering Outcomes for Industrial Networks
Why Industrial Problems Require a Different Solution Mindset
Enterprise IT networks are designed for flexibility and rapid change. Industrial networks are designed for continuity, predictability, and longevity - where downtime has physical consequences and latency equals risk.
Applying IT assumptions to operational technology (OT) environments introduces fragility. Failures occur not because technology is inadequate, but because it is applied without respect for operational constraints: deterministic timing, environmental harshness, safety integration, and decades-long lifecycles.
Throughput Technologies solutions begin with this recognition. We focus on the systemic causes of failure - timing uncertainty, unmanaged access, brittle architectures, and blind operation - and engineer outcomes that make networks predictable, resilient, and observable.
Solutions as Engineered Outcomes, Not Products
A solution is not a device; it is the guaranteed behaviour a network exhibits under stress, failure, and attack-validated, measured, and trusted over time.
This outcome-based framing changes the conversation from features to operational proof:
- Redundancy is not two links; it is guaranteed recovery within 50 milliseconds.
- Security is not a firewall; it is enabling only the right access, under control, without disrupting operations.
- Diagnostics are not dashboards; they are early visibility into degradation, enabling intervention before failure.
- Determinism is not speed; it is bounded latency and predictable behaviour under all conditions.
The Six Core Solution Domains
Each domain addresses a distinct class of industrial network failure. They are designed to interlock, creating a cohesive architectural defence against operational risk.
1. Industrial Ethernet Networks
Architectures that enforce deterministic behaviour, traffic separation, and environmental resilience for control and safety systems. The foundation upon which all other solutions depend.
Outcome: Predictable network performance under industrial load, failure, and maintenance.
3. Secure Remote Access
Controlled, session-based access models that replace risky VPNs, enabling maintenance and support without introducing standing trust or compromising determinism.
Outcome: Necessary connectivity without exposing the operational network to compromise or instability.
5. OT Cybersecurity
Security controls designed for operational continuity - segmentation, anomaly detection, secure boundaries - that align with safety and timing requirements.
Outcome: Contained risk and preserved safety without disrupting the deterministic operation of critical systems.
2. Fibre Optic Communications
Engineered physical layer infrastructure for long-distance, noise-immune backbones designed for harsh environments, with built-in fault localisation and lifecycle durability.
Outcome: A stable, observable physical foundation that survives decades of environmental and operational stress.
4. Network Redundancy & Resilience
Architectures designed to preserve operation through failure, with deterministic recovery, deliberate diversity, and validated failover behaviour.
Outcome: Continuous operation within defined limits, even during component or path failures.
6. Network Diagnostics & Monitoring
Proactive visibility that transforms networks into observable systems, enabling fault location, trend analysis, and predictive maintenance.
Outcome: Evidence-based understanding and intervention, replacing reactive troubleshooting with confident management.
How the Solutions Interlock and Reinforce Each Other
No industrial problem is solved by a single solution domain. Resilience emerges from their deliberate integration.
Isolated solutions create fragile point fixes. Engineered together, they create a defensible architecture:
- Diagnostics validate Redundancy: Monitoring proves that failover mechanisms perform within their designed time bounds.
- Secure Access depends on Segmentation: Zero-trust remote access requires clearly defined security zones to enforce policy.
- Deterministic Ethernet enables effective Monitoring: Predictable traffic patterns create a stable baseline for anomaly detection.
- Resilient Fibre supports Determinism: A stable physical layer is prerequisite for bounded latency and low jitter.
- Cybersecurity relies on Visibility: You cannot defend a network you cannot see; diagnostics provide the essential baseline.
Architectural Principle: Solutions are most effective at the intersections. The goal is not to deploy six independent tools, but to engineer a cohesive system where each domain reinforces the others.
Mapping Solutions to Operational Reality
While the solution domains are consistent, their application varies by industry, driven by unique operational constraints and risk profiles.
Rail networks prioritise deterministic Ethernet and rugged fibre for trackside communications. Utilities focus on wide-area resilience and secure access for remote substations. Manufacturing requires segmentation and diagnostics to maintain production continuity. The underlying principles remain the same; the implementation is tailored.
The Industries section shows where problems occur. This Solutions section explains how they are engineered away. Your path starts by identifying which failure modes dominate your environment.
A Guidance-Led Engagement Model
Throughput Technologies does not lead with products or prescriptive designs. We begin with questions that clarify operational risk and desired outcomes.
Our engagement starts by understanding:
- What must never fail, and what are the consequences if it does?
- What network behaviour must be guaranteed (latency, recovery time, availability)?
- What external access is unavoidable, and how can it be controlled?
- How must the network adapt over its expected 15–20 year lifecycle?
Solutions follow from these answers. If you are unsure which domain to address first, that uncertainty is the starting point for a structured assessment.
Navigate to the Solution Pages
Engineering deterministic behaviour and predictable performance for control and safety systems in operational environments.
Designing long-life, resilient physical layer infrastructure for harsh, distributed industrial environments.
Architecting controlled, auditable connectivity for maintenance and support without compromising operational safety or stability.
Designing networks that continue to operate predictably during component or path failures through deterministic recovery.
Implementing security controls that protect operational continuity and safety without disrupting deterministic network behaviour.
Building proactive visibility to understand network behaviour, locate faults, and enable predictive maintenance.
Industrial network success is defined by predictable outcomes,
Talk with a Solutions Specialist
to map your operational risks to the appropriate solution domains and define a path grounded in evidence, not speculation.