Highway Communications Backbone Networks
Designing resilient fibre and wireless backbone infrastructure for intelligent transport systems along highway corridors with appropriate redundancy.
Traffic management centres integrate video surveillance, signal control, incident management, and traveller information – requiring networks that deliver real-time data for decision-making while surviving peak loads during incidents.
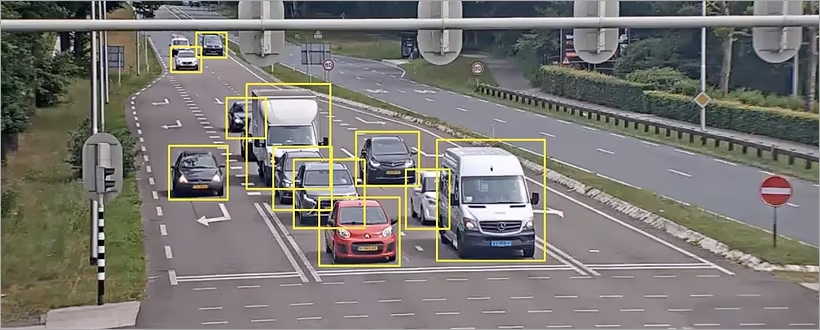
Traffic management centre networks experience peak loads during incidents when multiple systems activate simultaneously – network design must accommodate these bursts without performance degradation.
During major incidents, operators access multiple camera feeds, activate variable message signs, adjust signal timings, and coordinate with emergency services. Network traffic increases dramatically. Inadequate design leads to delayed video, slow control response, and missed coordination opportunities.
Effective TMC network design starts with understanding peak simultaneous loads. Architecture implements appropriate capacity, quality of service (QoS), and redundancy. Integration requirements between systems add complexity – data must flow reliably between video, control, and information systems.
The network is the central nervous system of the TMC. A failure here doesn't just affect one function; it can blind operators to road conditions, paralyse signal control, and sever communication with field personnel and partner agencies simultaneously. Therefore, resilience is not a feature but a fundamental design requirement. This involves building redundancy not just in hardware but in data paths, power feeds, and even geographic location for disaster recovery.
Segmented TMC networks separate video, control, and data systems for security and performance.
Traffic management centre networks segment different traffic types – video, control signals, data – to ensure security and performance while enabling necessary integration.
Video surveillance generates high-bandwidth continuous traffic. Signal control requires deterministic timing. Data systems handle traveller information and historical records. Each has different network requirements.
Segmentation uses virtual local area networks (VLANs) with appropriate quality of service (QoS) policies. Firewalls control traffic between segments. The design balances separation for security with integration for operational coordination.
A typical segmentation strategy includes separate VLANs for: Operator Workstations, CCTV Video Streams, SCADA/Control Traffic (for signals and signs), ITS Data (from sensors and detectors), Corporate/IT Systems, and a DMZ for external partners (e.g., emergency services, media). This logical separation prevents a broadcast storm or security breach in one domain from cascading to critical control systems. However, strict segmentation can hinder operational workflows. Throughput Technologies designs controlled integration points—such as application-layer gateways or data diodes—that allow specific, authorised data flows (like sending a camera stream to an operator console) without merging the networks.
Traffic signal supervisory control and data acquisition (SCADA) systems require deterministic networks for coordinated signal timing, with reliability directly affecting traffic flow efficiency.
Signal controllers operate on fixed timing cycles. Network delays affect coordination between intersections. Modern systems adjust timing based on traffic conditions, requiring reliable data exchange.
Network design guarantees maximum latency for control signals. Redundancy ensures continuous operation. Security prevents unauthorised access that could disrupt traffic flow. Integration with other systems enables adaptive control strategies.
The choice of SCADA protocol (e.g., DNP3, Modbus TCP/IP, or vendor-specific protocols) influences network design. Some protocols are chatty, generating frequent small packets, while others operate on poll-response cycles. The network must handle this traffic without introducing jitter (variance in latency), which is more damaging to signal coordination than a slightly higher but consistent delay. We design networks with priority queuing and traffic shaping to ensure SCADA packets are never delayed by bulk data transfers like video or file backups.
Furthermore, the SCADA network must be secure yet accessible for maintenance. We implement robust network access control (NAC) and segment field maintenance ports. Remote access for vendors is provided through secure, audited, and temporary VPN tunnels rather than permanent open connections, aligning with the principle of least privilege.
Large-format video walls display multiple information sources – network design must deliver high-resolution content without latency or synchronisation issues.
Video walls show camera feeds, maps, data visualisations, and alerts. Each source requires network delivery to display processors. Multiple high-resolution streams need significant bandwidth.
Network architecture uses 10 GbE or higher backbone connections. Quality of service (QoS) prioritises video traffic. Multicast efficiently delivers same streams to multiple displays. Frame synchronisation prevents visual artifacts.
The key challenge is avoiding packet loss. Even a 0.1% packet loss can cause noticeable glitches, freezing, or macroblocking on a video wall, distracting operators during critical incidents. This demands a lossless or near-lossless network fabric. Technologies like Data Centre Bridging (DCB) with Priority Flow Control (PFC) can be applied in high-performance TMC networks to create a converged Ethernet fabric that guarantees bandwidth and eliminates loss for video traffic. Additionally, the source-to-display path must be optimised. We recommend decoding and scaling video at a central media server rather than at the wall controller, sending only the finalised visual layer to reduce network load and processing latency.
TMC networks integrate with public transport and emergency services for coordinated response.
Traffic management centres coordinate with public transport operators and emergency services – network design enables secure information sharing while maintaining system separation.
During incidents, emergency services need traffic camera access and route clearance. Public transport requires priority signalling and incident information. Coordination improves response effectiveness.
Integration uses controlled gateways rather than network merging. Secure data exchange platforms share specific information. Role-based access controls determine what each agency can see. Testing during exercises validates coordination.
A common model is a "Situation Room" network segment or a dedicated collaboration portal. External agencies authenticate to this platform via secure VPNs or client software. The TMC network pushes curated data—such as a GeoJSON feed of incident locations, selected camera streams (not all), and road closure polygons—to this portal. This is far more secure and scalable than giving external entities direct access to internal SCADA or video management systems. The network design must ensure this outgoing data flow does not impact internal performance and is protected by egress firewalls and intrusion prevention systems.
Remote access enables off-site monitoring and management – requiring secure connectivity that doesn't compromise centre security or network performance.
Managers, engineers, and support personnel need remote access for monitoring, maintenance, and emergency response. Traditional virtual private network (VPN) approaches create security risks.
Secure remote access solutions use zero-trust principles: each session authenticated and authorised for specific systems only. Session monitoring provides audit trails. Integration with existing identity management simplifies administration.
Modern solutions move beyond network-level VPNs to application-level access. A zero-trust network access (ZTNA) model assumes no user or device is trusted by default, regardless of location. Users connect to a broker that grants access only to authorised applications (like the CCTV interface or signal control software), not the entire TMC network. This significantly reduces the attack surface. The network infrastructure must support this by allowing granular traffic steering and providing detailed logs for compliance and forensic analysis. Throughput Technologies helps implement these models, ensuring that remote convenience does not come at the cost of security.
Continuous network monitoring detects issues before they affect operations – providing visibility into performance, security, and availability across TMC systems.
Network problems can affect multiple TMC functions simultaneously. Proactive monitoring identifies degradation before failure. Correlating network events with operational issues speeds troubleshooting.
Monitoring covers infrastructure, performance, and security. Thresholds alert on abnormal conditions. Integration with ticketing systems automates incident creation. Regular reporting identifies trends for capacity planning.
Effective monitoring is contextual. It's not enough to know a switch port is up; you need to know if the camera connected to it is streaming usable video. We implement monitoring that correlates network metrics (bandwidth, latency, packet loss) with application health checks (video stream integrity, SCADA poll success rate). This holistic view allows operators to distinguish between a network failure, a field device failure, and an application server problem instantly. Dashboards should be tailored to different roles: network engineers see topology and device health, while traffic operators see the status of the systems they directly rely on.
Throughput Technologies advises on traffic management centre network architecture that balances real-time performance requirements with security and integration needs. Our designs ensure that when an incident occurs, the network is a facilitator of response, not a point of failure.
Talk with a Solutions Specialist to design your traffic management centre network infrastructure.
A video wall displaying 20 simultaneous 1080p streams needs 300–500 Mbps continuous bandwidth. 4K streams increase this to 600–800 Mbps. Burst traffic during layout changes adds temporary peaks. Dedicated 10 GbE backbone links are now standard for major centres. Edge processing reduces bandwidth by decoding at source and transmitting only needed display regions. For future-proofing, design the core switching fabric to support 25 GbE or 40 GbE uplinks, as video resolution and wall sizes will only increase.
Signal control typically needs 100–300 millisecond round-trip latency for coordinated timing. Adaptive systems using real-time traffic data may tolerate slightly longer delays. The critical factor is consistency – variable latency (jitter) affects coordination more than slightly higher but consistent latency. Network design must guarantee maximum latency under worst-case conditions. This often requires implementing strict QoS policies and ensuring network convergence times (after a link failure) are within the control system's tolerance.
Use secure video sharing portals rather than direct network access. Emergency services authenticate to a gateway that streams specific cameras based on incident location and responder role. Session recording provides audit trails. Access expires automatically after incident resolution. The system should integrate with emergency dispatch systems to automate camera selection based on incident location. Furthermore, the shared streams should be watermarked and lower resolution to protect privacy and manage bandwidth, while providing sufficient situational awareness.
Critical systems need dual diverse fibre entry routes, redundant core switches with hot standby, and uninterruptible power with generator backup. Video systems may tolerate brief interruptions during failover; signal control needs continuous operation. Geographic redundancy to a backup centre provides disaster recovery. Test failover regularly – untested redundancy often fails when needed. Consider also the "split-brain" scenario: design the network and applications to handle a scenario where both primary and backup sites think they are active, to avoid data corruption or conflicting control commands.
Monitor at multiple levels: infrastructure (switch ports, link status), performance (bandwidth utilisation, latency), application (video stream quality, control response times), and security (unauthorised access attempts). Set thresholds based on normal operation baselines. Correlate network events with operational issues – if multiple cameras drop simultaneously with network errors, the cause is likely network rather than cameras. Regular reporting identifies trends for capacity planning. Implement a Security Information and Event Management (SIEM) system to aggregate logs from network devices, servers, and applications for advanced threat detection and compliance reporting.
Designing resilient fibre and wireless backbone infrastructure for intelligent transport systems along highway corridors with appropriate redundancy.
Networking for electronic toll collection, violation enforcement, and toll plaza communications with reliability requirements for revenue collection.
Protecting transportation networks from cyber threats while ensuring operational continuity through segmentation, secure access, and resilient design.